On March 19, a threat actor calling themselves “TeamPCP” compromised Trivy, Aqua Security’s open-source vulnerability scanner. They injected credential-stealing malware into official releases and hijacked the project’s GitHub Actions workflow. Every CI/CD pipeline running Trivy was potentially exposed.
Think about that for a second. The tool that organizations run specifically to check whether their code has security problems was itself turned into a security problem. It scanned your pipeline, and while it scanned, it harvested credentials.
What Happened
The attack targeted the `aquasecurity/trivy-action` repository, the official GitHub Action that millions of developers use to run Trivy scans inside their CI/CD pipelines, according to reports from Wiz Research and Socket. The attacker force-pushed 75 out of 76 version tags in the repository, replacing them with a compromised release (version 0.69.4) that contained credential-stealing malware.
75 out of 76 tags. The attacker didn’t slip something into the latest release and hope people would update. They rewrote the project’s entire version history. Any pipeline pinned to almost any version of trivy-action would pull down the compromised code on its next run.
The commits were spoofed to look like they came from legitimate maintainers. The attacker impersonated the GitHub user rauchg (associated with actions/checkout) and DmitriyLewen (a Trivy maintainer), according to CrowdStrike’s investigation. Someone went through the effort of making the malicious commits look routine.
The compromised release also triggered what researchers are calling CanisterWorm, a self-spreading payload that propagated across 47 npm packages, according to Socket’s analysis. So the blast radius extended well beyond just Trivy users.
The Detection Story vs. the Damage Story
Every writeup so far focuses on the technical mechanics and who caught it. That story is told. The story nobody is telling is the damage assessment.
Independent security researcher Paul McCarty was the first to flag the compromise, before CrowdStrike, before Wiz, before any of the platforms that sell supply chain monitoring as a service. CrowdStrike subsequently traced the activity after detecting a spike in anomalous script execution across their Falcon platform customer base. Wiz Research and Socket published detailed technical analyses. But the initial catch was manual. Human eyeballs on a git log, noticing something that didn’t look right.
Good. It got caught. But the compromised tags were live for hours before McCarty flagged them. During those hours, how many CI/CD pipelines ran? How many credentials were harvested? How many organizations are still running a cached compromised version without knowing? Nobody has published numbers. No vendor has released an impact estimate. The detection story has been covered exhaustively. The actual damage remains completely unquantified.
That gap should bother people more than it seems to.
One Researcher, Three Billion-Dollar Companies
Post-SolarWinds, enterprises poured money into supply chain security tooling. Automated monitoring. Real-time dependency scanning. Vendor risk platforms. Billions in aggregate spend. And when a threat actor rewrote 75 version tags on one of the most widely used security actions on GitHub, the first person to notice was one independent researcher doing manual review.
This isn’t an indictment of CrowdStrike, Wiz, or Socket. They all responded quickly once alerted and produced strong technical analysis. But it raises a structural question about what automated supply chain monitoring actually detects. These systems are built to flag known vulnerability patterns, malicious package publications, suspicious dependency changes. A tag rewrite that replaces existing, trusted versions with malicious ones may simply fall outside the pattern set that automated tools are trained to catch. It looks like a legitimate release. Because it used to be one.
There may be an entire class of supply chain attack that only humans can catch, because the attack vector is social (spoofed identities, rewritten history) rather than technical (malicious code signatures, unusual network calls). If that’s true, enterprises are paying for monitoring that covers one half of the threat surface and leaving the other half to luck and the goodwill of independent researchers.
The Tag Mutability Problem
The 75-out-of-76 tag rewrite exposes something that should have been fixed years ago.
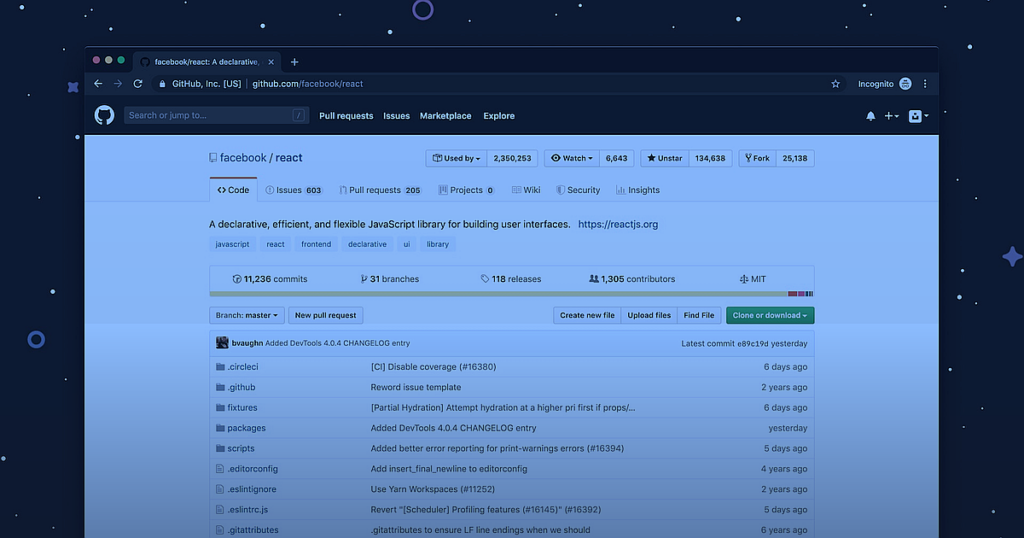
Standard practice for pinning GitHub Actions is to reference a version tag. You write `uses: aquasecurity/trivy-action@v1.2.3` and assume that tag points to the same code it always did. But Git tags are mutable. They can be force-pushed. When TeamPCP overwrote those tags, every pipeline referencing any of them started pulling down malicious code on its next run. No notification. No indication anything changed.
GitHub supports pinning actions by commit SHA, which is immutable and would have been resistant to this attack. Almost nobody does it. It’s ugly, it’s hard to maintain, and most teams don’t consider the threat model where an action’s entire tag history gets rewritten overnight.
After this, they should. And GitHub should be asking itself whether mutable tags are a sane default for a system that runs arbitrary code in millions of CI/CD pipelines.
What This Actually Means
Supply chain security tools are only as trustworthy as their own supply chain. That’s a circular problem with no clean solution.
Pin your GitHub Actions by commit SHA, not by version tag. Audit the permissions your CI/CD pipelines grant to third-party actions. Treat your security tooling with the same suspicion you’d treat any other third-party dependency, because to an attacker, a vulnerability scanner with elevated access is the best possible target.
But the harder question is the one the industry doesn’t want to sit with. We know it got caught. We don’t know what it cost. And the fact that one person beat three of the biggest names in security to the detection should prompt some honest reflection about what automated supply chain monitoring is actually buying.
—
Lamar covers cybersecurity, enterprise tech, and the systems that shape how power and technology interact. Follow Laterstack for critical analysis of the stories that matter.